My Blogs
blog
Keep up with the latest news
AD - Administrative Limits
Active Directory Database limits restricts your ability to manage objects - Learn how to quickly fix the problem
I recently ran into an issue with a particular environment where Active Directory and PKI services were deployed. One of the service accounts which I was attempting to ‘unlock’ refused to co-operate and instead offered the most unhelpful message. Administrative limit for this request was exceeded - this was not my first time encountering the message, previously this haunted me while I was managing a Windows PKI infrastructure and with some quick searches, confirmed my initial suspicion.
Read moreBicep - Tags as Parameters
Deploying infrastructure ARM Templates to Azure, but using Tags and their respective value as the parameter configuration settings
In a post earlier, we look at using arm to lookup the value of tags' at both the Subscription and Resource Level. With Bicep this is much easier to understand. This is the same lab configuration as in the original post, but this time to code should be a lot more readable. // Sample to lookup tag values // Both Subscription and Resource Level @description('The resource ID of the resource we wish to look up a tag from.
Read moreStreaming Vynil On Sonos
Mixup some Vyinl Oldies, a little Ice to cast, and a PI for some energy, and your ready to go
A little known trivia - I was once a Disc Jokey, and spent a lot of my youth behind the decks, in clubs around the West Of Ireland. Today, I still am the proud owner of a very large collection of Vynil and CD music, which of course deserves to get a second life with my digital streaming audio system powered by Sonos USB Turntable Streamer I own a really nice turntable which is modeled on the Legendary Technical SL1200 MK3, which I am so well aquatinted with, including the awesome Citronix DJ Console which was home to 2 of these beauties in so many clubs way back when…
Read moreAzure IaC - Tags as Parameters
Deploying infrastructure ARM Templates to Azure, but using Tags and thier respective value as the parameter configuration settings
In the post, I am going to introduce a concept which will allow you to greatly up your Infrastructure as Code game, by using Azure as a State Machine! One of the typical challenges when deploying ARM templates, is the sheer number of parameters which we find as a requirement to complete a deployment; which as you will appreciate gets considerably harder as we target many environments. There are a number of methods to address this, including the use of Parameter files or Continuous deployment variables; each with their own challenges.
Read moreChange Detection using Oxidized
Oxidized is a Linux based service which has the ability to monitor a device’s configuration, including software and hardware. Current configuration is backed up from each device and stored to a GIT repository to maintain history of changes.
The process is very simple: Login to each device in the router list router.db, Run Commands to get the information that will be saved Clean the output Commit the Changes to GIT Repository The tool is coded in Ruby, and implements a Domain Specific Language (DSL) for interaction. Finally, there is a Web based User experience included in the solution so we can get a fast overview of the world.
Read moreAzure Functions Scaffolding
Dependency injection is an approach to solve inversion of control that facilitates components that are easier to test and mock. To better understand dependency injection, this article walks through the creation of a simple DI framework and explains step-by-step how it works.
Most of my time is spent working on Governance in Azure; and while the cloud native plumbing is amzaing, there are still some gaps which need to be filled, and my go-to tool of choice is Azure Functions. One of the products which I oversee the devleopment of is called the ‘Concierge’ and recently maintaining it has been a challange instead of a joy. It was architected with Fuctions v1 principals, and its well time for a look inside the tool box.
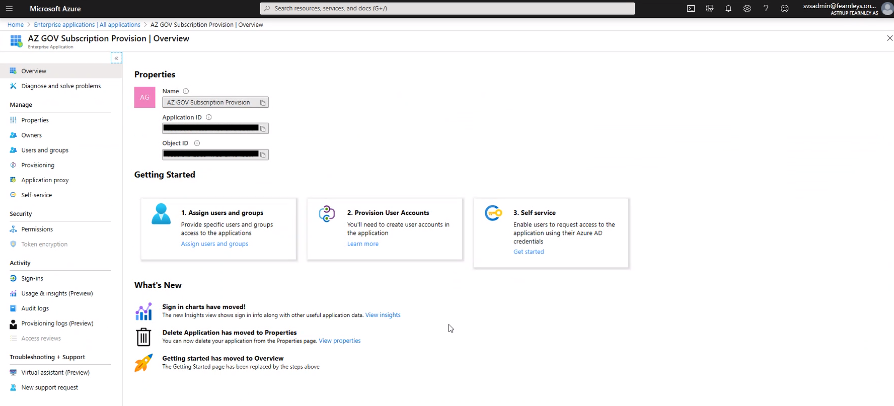
Read moreAzure EA - Delegating Privileges
Delegating Azure Enterprise Agreement Owner privileges to a Service Principal (SPN)
EA Department / Account Administrator
Under the Enterprise agreement we have some different Persona’s, which have quite different abilities and operations upon which they are permitted to preform.
Before we being the process of delegation, It is important to understand this Hierarchy, so we can correctly proceed with the technical work ahead.
Read moreAzure IaC - Function Keys
Retrieve the Function Host Keys while deploying an ARM template
Todays conundrum: As I deploy a new Function Application, I need a simple methodology to retrieve the Host Keys for the function application so that I validate the deployment has been successful; and potentially pass on the key to related services, for example API Management.
As before, I am leveraging templates, and will stay cloud native; this time depending on the functions Output ability to present the keys.
Read moreAzure IaC - Appending Tags
Dynamically appending Tags to our ARM template with the union function
Todays conundrum: As I am leveraging templates, there will always be some standard tags I require to implement within the template, but I also require to provide additional tags as a parameter to be appended with the deployment. My objective is to set up tags within an ARM template in accordance with good governance and the Cloud adoption framework. Solution ARM Template functions to the rescue. Todays salvation is called union, which you can learn more about on the actual [reference site][https://docs.
Read moreIgnite 2019 - Web Application Gateway and Firewall
Delivering PaaS Services Privately on Azure VNets with Private Link
Ignite Session: BRK3169 Presenter: Amit Srivastava Mission Critical HTTP Applications, there are many things to consider Personalized, Micro-Services, Rich Context…. To support this MS have a number of services i the Suite - Azure Frontdoor, Application Gateway, Azure CDN, Web Application Firewall, Azure Load Balancer, and Azure Traffic Manager Azure Application Gateway Regional Gateway as a service Feature Description Platform managed Built in high availability and scalability) Layer 7 balancing URL Path, Host based, round robin, session affinity, redirection Security and SSL management WAF, SSL Offload, SSL Re-Encryption, SSL Policy Public or ILB Public, Internal or Both Flexible backends VMs, VMSS, AKS, Public IP, Cloud Services, ALB.
Read more- Page 1 of 4
- Previous Posts